15 Hackers You Hope Your Computer Never Meets

In the world of cybersecurity, there are individuals whose names strike fear into the hearts of even the most seasoned professionals. These are the hackers who have breached the defenses of some of the world's largest organizations, stolen sensitive information, and caused untold damage. In this book, we profile 15 of the most notorious hackers in history, exploring their techniques, their motivations, and the impact of their actions. From Kevin Mitnick to Anonymous, these are the hackers you hope your computer never meets.
4.4 out of 5
| Language | : | English |
| File size | : | 1544 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 170 pages |
| Lending | : | Enabled |
1. Kevin Mitnick
Kevin Mitnick is one of the most famous hackers in the world. He was first arrested in 1981 for hacking into the North American Air Defense Command (NORAD) computer system. In 1983, he was arrested again for hacking into the Pacific Bell computer system. Mitnick served five years in prison for his crimes.
Mitnick is a brilliant hacker who has used his skills to exploit vulnerabilities in computer systems. He has stolen sensitive information, including credit card numbers and social security numbers. Mitnick has also been accused of hacking into government computer systems.
Mitnick is now a security consultant and author. He has written several books about computer security, including "The Art of Deception" and "Ghost in the Wires." Mitnick is also a sought-after speaker at cybersecurity conferences.
2. Anonymous
Anonymous is a decentralized international activist and hacktivist collective. The group has been involved in a number of high-profile cyberattacks, including the attacks on the Church of Scientology and the Sony PlayStation Network.
Anonymous is a loosely organized group of individuals who use the internet to coordinate their activities. The group's members are often motivated by a desire to expose corruption and injustice. Anonymous has been credited with helping to bring about the Arab Spring and the Occupy Wall Street movement.
Anonymous is a powerful force in the world of cybersecurity. The group's members are skilled hackers who have access to a vast network of resources. Anonymous is a major threat to organizations that are not prepared for cyberattacks.
3. Albert Gonzalez
Albert Gonzalez is a Cuban-American hacker who was sentenced to 20 years in prison for his role in the TJX Companies data breach. The TJX Companies data breach was one of the largest data breaches in history, affecting over 100 million customers.
Gonzalez used a SQL injection attack to gain access to the TJX Companies' computer systems. He then stole credit card numbers and other sensitive information from the company's databases.
Gonzalez is a skilled hacker who has used his skills to steal millions of dollars from businesses and individuals. He is a major threat to organizations that are not prepared for cyberattacks.
4. Adrian Lamo

Adrian Lamo is an American hacker who was known for his high-profile hacks of The New York Times and Microsoft. Lamo was sentenced to two years in prison for his crimes.
Lamo is a skilled hacker who has used his skills to expose vulnerabilities in computer systems. He has also been accused of hacking into government computer systems.
Lamo is now a security consultant and author. He has written several books about computer security, including "The Hacker's Handbook" and "The Art of Deception." Lamo is also a sought-after speaker at cybersecurity conferences.
5. Michael Calce
Michael Calce is a Canadian hacker who was known as "MafiaBoy." Calce was arrested in 2000 for launching a series of distributed denial of service (DDoS) attacks against several high-profile websites, including Yahoo! and CNN.
Calce was sentenced to eight months in prison for his crimes. He was also Free Downloaded to pay $1 million in restitution to the victims of his attacks.
Calce is a skilled hacker who has used his skills to cause significant damage to businesses and individuals. He is a major threat to organizations that are not prepared for cyber
4.4 out of 5
| Language | : | English |
| File size | : | 1544 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 170 pages |
| Lending | : | Enabled |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Sean Jensen
Sean Jensen Tom Swimm
Tom Swimm Sharon C Cooper
Sharon C Cooper Hanna Sandvig
Hanna Sandvig Samuel Decalo
Samuel Decalo Jillian Dodd
Jillian Dodd Gj Kelly
Gj Kelly Ed Rosenthal
Ed Rosenthal Zain E Asher
Zain E Asher Van Hoang
Van Hoang Stuart Laing
Stuart Laing Suzanne Anderson
Suzanne Anderson Theodore Kekstadt
Theodore Kekstadt Shanterra Mcbride
Shanterra Mcbride Stacy Lynn Harp
Stacy Lynn Harp Tya Marie
Tya Marie Shan Ling Li
Shan Ling Li Stephanie Dray
Stephanie Dray Tim Kimmel
Tim Kimmel Kami Garcia
Kami Garcia
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Cole PowellFollow ·12.5k
Cole PowellFollow ·12.5k Holden BellFollow ·14.9k
Holden BellFollow ·14.9k Art MitchellFollow ·14k
Art MitchellFollow ·14k Jeffery BellFollow ·3.6k
Jeffery BellFollow ·3.6k Carlos DrummondFollow ·3.1k
Carlos DrummondFollow ·3.1k Drew BellFollow ·2.1k
Drew BellFollow ·2.1k Cristian CoxFollow ·18.4k
Cristian CoxFollow ·18.4k Albert CamusFollow ·17.1k
Albert CamusFollow ·17.1k
 Amir Simmons
Amir SimmonsImmerse Yourself in the Enchanting Realm of Nora Roberts'...
Prepare to be captivated by...
 Dan Henderson
Dan HendersonUnleash the Explosive Action of Going Ballistic Combined...
Prepare for an...
 Jeffery Bell
Jeffery BellDiscover the Controversial and Captivating "The Anarchist...
In the realm of literature, there are...
 Ryan Foster
Ryan FosterUnveiling Lincoln's Eloquence: How His Greatest Speeches...
In the annals of American...
 Jaime Mitchell
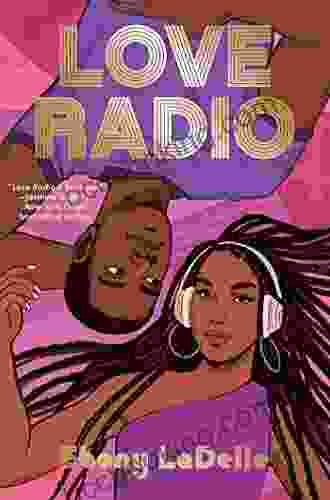
Jaime MitchellLove Radio Vinny Berry: A Journey of Heartbreak, Healing,...
Vinny Berry's...
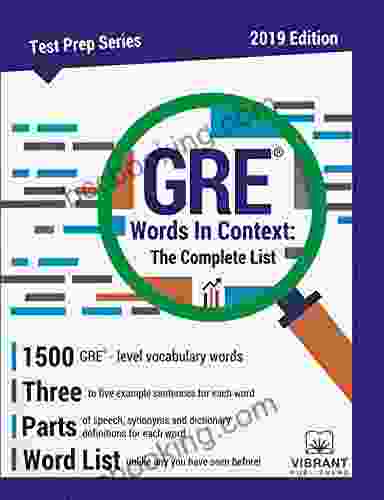
4.4 out of 5
| Language | : | English |
| File size | : | 1544 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 170 pages |
| Lending | : | Enabled |